
What is CIAM? The Ultimate Guide to a Secure, Scalable, and Streamlined Customer Experience
In today’s digital landscape, businesses of all sizes and industries are increasingly relying on digital channels to interact with customers.
As a result, managing customer identities and access has become a critical business requirement. This is where Customer Identity and Access Management (CIAM) comes in.
What is CIAM?
CIAM is a subset of identity and access management (IAM) that focuses on managing the digital identities and access controls of customers as opposed to employees.
CIAM solutions provide a centralized platform for organizations to manage their customer’s identities, preferences, and consent across various digital touchpoints like websites, mobile apps, and social platforms.
The CIAM solution of an organization is what allows customers to safely sign up and log into online applications and services and manage their accounts, profiles, and security settings.
The main objective of a CIAM solution is to deliver a great customer experience while protecting customer data.
Key Elements of CIAM
Self-Service Registration and Account Management
The most important element of any CIAM solution is the ability for a user to sign up for your service by themselves. Making this process streamlined and intuitive for potential customers is critical.
Considering that the average conversion rate of a website in 2022 was 3.65%, avoiding any inconveniences during registration that may deter visitors from completing the sign-up process need to be considered and avoided at all costs.
Personalization
CIAM solutions enable organizations to offer personalized experiences to customers based on their preferences and behaviors.
This also allows users to manage their accounts themselves to update information like their email, home addresses, security, and consent preferences.
Any CIAM solution also has to allow users to reset passwords and go through authentication protocols without involving an IT professional.
Centralized Customer Profiles
Having customer profiles that are centralized across applications and devices is a key element of CIAM.
This allows users to update their details in one interface and those details be updated on all interfaces, removing any data silos and preventing frustration or duplicate work for the customer.
Scalability
Particularly when operating within a large enterprise, cybersecurity professionals have to be sure that the system is scalable and capable of handling potentially millions of users.
Take OpenAI for example – upon the release of ChatGPT, it amassed over 1,000,000 users in only 1 week.
Single Sign-On
Single sign-on (SSO) is a feature of CIAM being utilized very effectively by Google. It allows a user to sign into one application and automatically be signed into a suite of other applications.
For example, when a user signs into Gmail, they’re automatically signed into Youtube, Google Drive, and any other G-suite application.
Consent Management
In the digital-first, always-on society we live in, people want to be in control of their privacy preferences when they’re online.
CIAM solutions enable customers to manage their data privacy preferences and give explicit consent to data sharing and usage – a must for any organization handling customer data.
Multi-Factor Authentication (MFA)
MFA is a login procedure, often backed by artificial intelligence, that adds an additional layer of security in an attempt to prevent fraudulent logins. This is achieved by requiring a user to use more than one authentication method to gain access to a system.
This allows for a better means of accessing software, applications, and systems that’s much safer than the traditional username and password method that’s easy for hackers to exploit.
MFA is increasingly becoming regarded as a basic security requirement with more and more data privacy laws starting to demand it.
Modern CIAM supports AI-powered adaptive authentication which uses contextual behavioral analytics and administratively defined policies to decide what authentication is required under a specific set of circumstances.
Identity Verification and Fraud Prevention
To protect against fraudulent activities such as account takeover, fake account creation, and identity theft, robust identity verification and fraud prevention features are central to any comprehensive CIAM strategy.
With fraud at its highest level in the last 20 years – according to PwC’s 2022 report in which they stated 51% of organizations had experienced fraud in the last two years – the focus on fraud prevention has to be higher than ever to protect customers and companies.
The Importance of Getting Your CIAM Right
Adherence to Privacy Laws
Failing to meet data laws such as GDPR, CCPA, and HIPAA can be costly for an organization in terms of both finances and reputation.
Regulation authorities determine how an organization collects, stores, and shares personal data. In order to meet these legal requirements, your CIAM needs to be top of mind.
Acquire and Retain Customers
A lot of time, energy, money, and resources go into attracting new customers to a business.
One of the first interactions a user has with your business is the registration process which makes it a critical part of the customer acquisition journey – getting this process wrong isn’t an option for businesses in such a competitive landscape.
Likewise, if your system isn’t user-friendly causing inconvenience to customers on a daily basis – they’ll likely look elsewhere, increasing churn and reducing the lifetime value of each customer to direct hit your bottom line.
Improve User Experience
In a world where convenience is so important for consumers – getting your user experience right has never been more important.
There are no second chances when it comes to pleasing customers.
Hubspot reported that 88% of customers are less likely to return to a site after a poor user experience.
So how exactly does CIAM improve the user experience?
Registration
Making the registration process as seamless as possible avoids deterring potential customers right at the point of joining.
By enabling convenient registration options like social registration, and minimizing the information a customer requires when joining, the process can be as seamless as possible.
Authentication
CIAM solutions allow for a variety of multifactor authentication options, giving users the freedom to decide what authentication methods are most convenient for them.
Authorization
Solutions continuously authorize access using adaptive authentication. Variables such as device, location, behavior, and more are used to determine the risk of the current session throughout that session.
Varied methods of authorization can be deployed based on the level of risk.
For example, during low-risk conditions users may leave and return without signing in again. Opposingly, a user that is acting suspiciously may be required to re-authenticate – increasing the security of the user’s account.
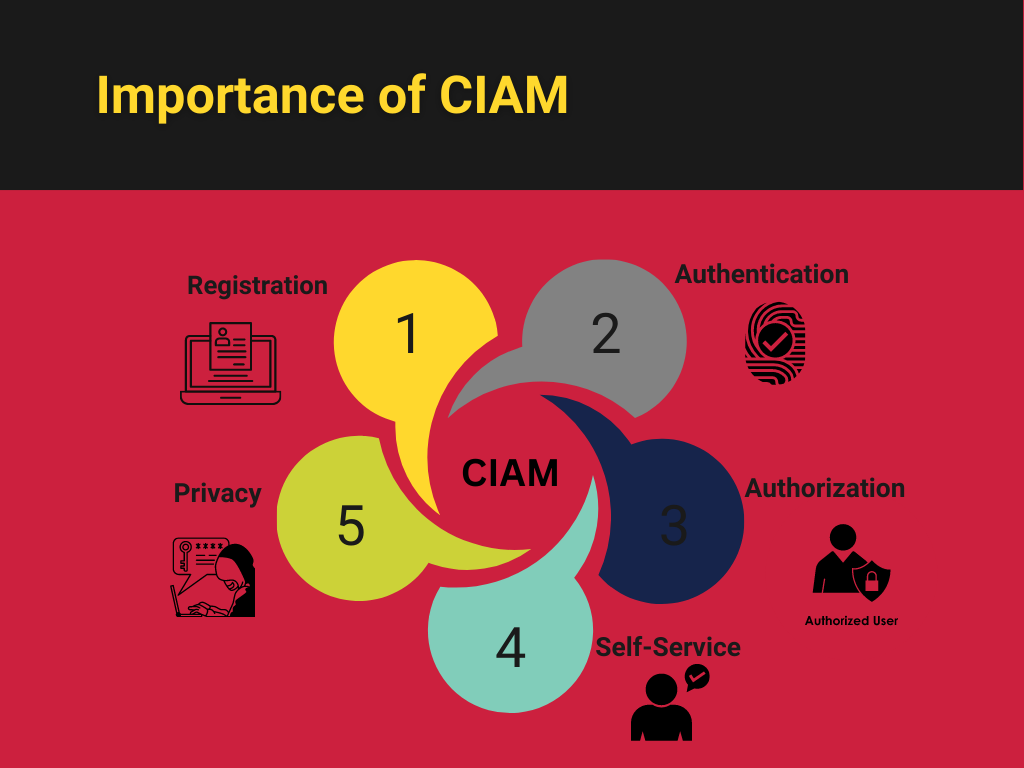
Self-Service
Tasks such as profile preference management, contact preferences, password reset, help requests, and security preferences should all be modifiable by the user manually.
This not only provides the user with a more seamless experience but relieves pressure on support teams.
Multichannel Support
Implementing an effective CIAM system ensures that users have fluidity between devices.
CIAM allows for flexibility on entry points across all devices, reducing the inconvenience to all users which ultimately increases the retention rates of customers.
Users expect their experience to be as fluid as the Apple ecosystem, in which they can access anything on any of their devices, from anywhere, anytime via their iCloud account.
This is the fluidity that users now expect in their experience with any company – and a comprehensive CIAM solution helps achieve this.
How is CIAM Different From IAM?
Most companies have some form of employee identity and access management, whether it’s swipe cards to access physical locations, usernames and passwords to access systems, or more complex passwordless authentication systems.
On the face of it, IAM and CIAM may seem the same. However, they actually have significant differences in terms of functionality.
Check out our article on CIAM vs IAM for a full breakdown
Employee vs Customers
This one might not be too much of a surprise but one of the main differences is that CIAM is focused on customer access to digital assets compared to IAM being primarily focused on employees.
User Experience
IAM is designed for employees who are familiar with a system meaning that the user’s experience isn’t usually top of mind when designing it.
CIAM however, is designed for non-technical users so being as user-friendly as possible is crucial.
Data Privacy
A great majority of measures that companies take to protect customer data with their CIAM strategy are driven by regulatory compliance requirements and restrictions.
Their IAM strategy is of course influenced by these regulations but is also driven by the need to protect intellectual property and combat other cybersecurity threats.
Performance and Scalability
For most enterprises, the rate of new customer onboarding is often much higher than the rate of new employee onboarding.
Arguably, this means the amount of data collected by a CIAM solution is exponentially greater than the amount of data collected by an IAM solution – millions of customers versus hundreds or thousands of employees.
Whether the system can handle that huge amount of data is crucial when choosing or designing your CIAM strategy.
Choosing the Right CIAM Solution
As explained above, getting your CIAM solution right is critical to the security and loyalty of your customers!
Getting it wrong could result in reduced conversion rates of prospects, existing customers seeking alternative solutions, hefty fines from regulation authorities, or your CIAM solution simply not being able to handle the volume of data.
Here are some factors to consider when choosing a CIAM solution:
Security: Security needs to be top of mind for a CIAM solution, without it you could land yourself in legal, financial, and reputation trouble. Features such as multi-factor authentication, encryption, and compliance with relevant data privacy regulations are essential.
User experience: Getting this wrong will simply mean fewer customers and reduced satisfaction. Ensuring that your CIAM solution is intuitive and user-friendly across multiple digital channels is non-negotiable.
Scalability: Your CIAM solution must meet demand and scale with your business as it grows. Look for a solution that can handle a high volume of users and is flexible enough to adapt to changing business needs.
Integration: Your CIAM solution has to be able to integrate seamlessly with your existing systems. Systems to consider are your CRM, marketing automation, and other backend systems.
Popular CIAM Vendors
There are several popular CIAM vendors in the market, each with its own strengths and weaknesses.
RediMinds recommends choosing one of the leading solutions:
Okta: A cloud-based identity management solution that offers network security solutions and provides a unified security infrastructure that allows for a seamless experience for users.
Transmit Security: Provide uncompromising security, fraud prevention, and customer experience with modular, orchestrated identity services.
RediMinds are a certified security implementation partner for both Okta and Transmit Security.
So, if you’re looking to improve your CIAM solutions then speak to one of our experts today.
