
Multi-Factor Authentication: How Safe Is Your Login Process?
The average consumer has 38.4 unique passwords to remember. So it’s unsurprising that 80% of data breaches are linked to weak passwords.
That’s why multi-factor authentication (MFA) is more important than ever in every company’s access management system to cut the risks posed by weak and repeated passwords.
Gartner anticipates that 60% of global enterprises will implement some kind of passwordless authentication method by the end of 2022 – boosting cyber safety, improving the user experience, and driving consumer confidence.
What is MFA?
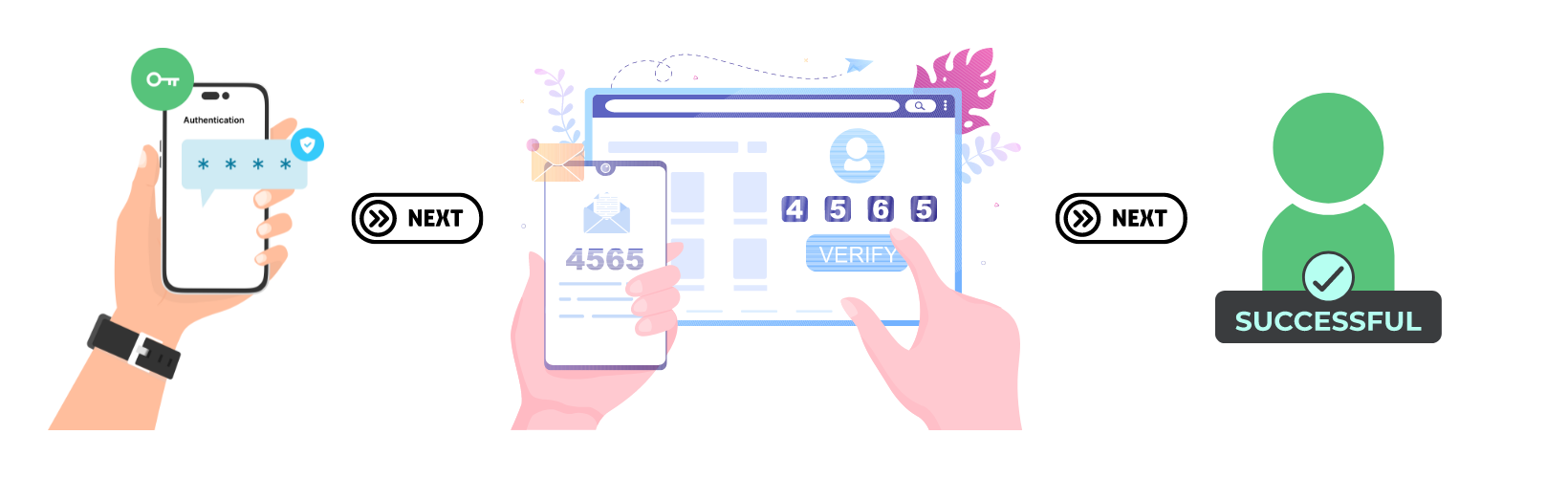
MFA is a login procedure, often backed by artificial intelligence, that adds an extra layer of security in an attempt to prevent fraudulent logins. This is achieved by requiring a user to use more than one authentication method to gain access to a system.
Right now, this is often a combination of a standard password and another authentication method. But, some companies have taken their digital transformation one step further and are progressing to complete passwordless authentication. This cuts out the use of standard passwords almost entirely, except as a fallback in case one of the passwordless authenticators fails.
Why is MFA So Important?
Technological advances don’t just benefit businesses in a positive way, they also benefit hackers as well – which can have disastrous consequences if businesses don’t remain a step ahead.
The standard ‘username and password’ login method is vulnerable to any number of attacks including:
- Credential stuffing: Testing lists from database breaches against multiple accounts to see if there are any matches
- Phishing: Hackers pretending to be from a reputable company coercing consumers to pass over their details
- Password spraying: testing a list of common passwords in an attempt to gain access to someone’s account e.g. 123456, password123, qwerty, 111111
- Keylogging: Recording keystrokes as a user types their login on a keyboard
- Brute force: Using an algorithm to obtain the password in plain text
- Local discovery: When a user writes down their password and it can be seen in plain sight
- Extortion
And the list goes on.
But, MFA is so effective that Microsoft claims despite 300 million fraudulent sign-in attempts every single day, it can prevent 99.9% of those attacks.
Methods of MFA
MFA can be broken down into four authentication methods:
- Knowledge: Something the user knows such as passwords, pins, and safety questions
- Ownership: Something the user has such as a safety token
- Biometrics: Something the user is such as fingerprints, retina, or voice recognition
- Location: Where the user is using their IP address and possibly geolocation
Multiple authentication methods lie within these 4 categories. Let’s examine seven of the most common MFA methods.
1. Push Notification Authentication
When a user attempts to log into a system or process a transaction, a notification is sent to an authorized device (usually their mobile phone) so the owner of the phone can confirm the login is legitimate.
Due to the number of logins and transactions made through mobile devices, this is often the easiest and most convenient method for users.
However, it does mean that if the user’s mobile device is compromised, so are their accounts. And from a company perspective, only those who have their own app can enable this type of authentication.
2. Mobile Application Code Authentication
Similar to push notifications, app authentication works by sending an OTP (One Time Password) to a 3rd party app such as Google Authenticator. The user must retrieve the OTP from the app on their authorized device to continue their login or transaction, usually in addition to their own password.
The key difficulty for businesses is in the implementation of this process, requiring experienced DevOps to integrate it into their systems.
3. SMS, Email, or Phone Token Authentication
Often, users receive the option to choose which method of token authentication they would prefer to use. They designate either:
- A cell phone number (usually their own) to which an OTP is sent via SMS upon every login attempt
- A cell phone number on which they’ll receive a phone call with a spoke OTP
- An email address to which they’ll receive the OTP
The limited lifetime of these passwords – usually only a few minutes- adds yet another layer of protection against fraud.
4. Physical Token Authentication
Physical token authentication is a “hard authentication” method, whereby the user must carry a physical item such as a swipe card or fob that generates an OTP for their login or transaction. For example, online transactions with some banks still require…
1) Online login details
2) Your debit card, and
3) A physical card reader to generate a transaction code
The downside? With so much of our online activity now on mobile devices, carrying a physical token can be inconvenient for users and easily lost. The cost to businesses of supplying these physical tokens can also be substantial.
5. Biometric Authentication
Arguably the safest method of authentication.
This is the process of using unique physical features to validate a user’s identity such as face recognition, fingerprints, and voice recognition.
Unlike standard passwords, biometric data is extremely hard to replicate and can’t be lost or stolen in the same way as standard passwords, which makes it unsurprising that it is quickly becoming the most popular form of authentication. Companies such as Apple and many banks have been leading the way on this and have already adopted it as a core part of their identity and access management strategy.
How to Implement MFA
Clearly, multi-factor authentication should be central to the security strategies of any company, for both their customers and employees. This can either support the traditional username and password login method as an additional layer of security or replace it entirely with passwordless authentication.
However, the implementation of artificial intelligence in cybersecurity is not straightforward. It requires specialist knowledge to successfully incorporate new authentication methods into existing systems without compromising the system, as well as ongoing maintenance and optimization to remain ahead of any threats.
If you need support to define and implement the right identity and access management solution for your organization, get in touch to speak with a RediMinds security specialist today.
Our team combines expertise in all of the core security solutions such as Transmit Security and Okta to support you from ideation to implementation.
Let’s create a safer online environment for your users, together.
